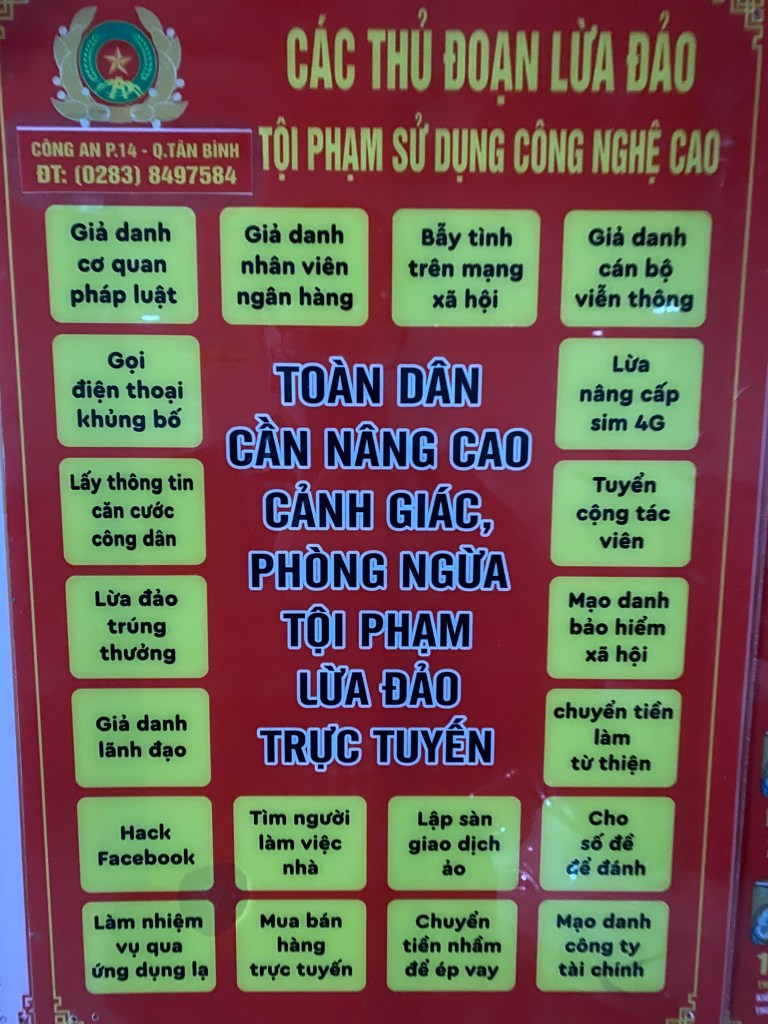
In the past, scams were often easy to spot: it can be suspicious messages, with poor grammar, or random strangers asking for money. Today, things are very different, it evolves!
Modern scammers use psychology, social engineering, AI-generated voices and videos, fake phone systems, and carefully planned trust-building strategies. Even smart, experienced people are getting tricked and losing tens or even hundreds of thousands of dollars.
This article breaks down several advanced scam techniques that are becoming increasingly common, and more importantly, how you can defend yourself and your family.
1. AI Voice & Video Impersonation Scams
One of the most dangerous new scam trends involves AI-generated faces and voices. Imagine receiving a message from a relative asking to borrow money urgently for a surgery! Naturally, you can become suspicious and decide to verify it with a video call. But during the call:
- You clearly see their face
- You hear their voice
- They speak naturally
- They say they need money to saving a life.
Everything looks real. Except it isn’t. Due to Social Networks and how careless people are using it, scammers can now:
- Collect photos and videos from social media
- Generate realistic facial movements from collected photos
- Clone person’s voice from video sounds
- Create short fake video calls or deepfake clips from AI-generated photos and sounds
This is possible because modern AI systems can now copy not only face expressions, but also eye movement, head pose, emotional tone from voice and conversational timing.
Warning signs
A major limit of AI generated content is latency. If the conversation get lagged above 300–500ms, human start feeling “off”. That’s why many “real-time” video calls from scammers are usually:
- Very short conversations & Excuses to avoid longer interaction: This is happen regularlry because scammer can’t predict what you will ask and there is not enough time to generate fake videos.
- Low resolution: If scammers decide to go with a long video calls and entrust AI to generate deepfake video & audio in realtime, they must have a very strong computer. Low resolution can be a solution to reduce the lag and feel “off”.
- Delayed audio synchronization & Awkward facial movement: Although AI can clone person’s voice and facial expression, it takes time to process so you can feel the delay in their responses.
In some cases, tiny details reveal the truth — such as outdated clothing, old work uniforms, or backgrounds that don’t match reality.
How to protect yourself
- Never trust a video call that borrow money.
- Call the person back via phone number, not Social Networks video calls.
- Ask unexpected questions only the real person would know.
AI impersonation technology is improving rapidly. Verification habits must improve too.
2. Relationship-Based Business Scams
Some scams are no longer random attacks. They are long-term psychological operations.
The setup
A scammer spends weeks or months building trust with someone online by:
- Buying products normally
- Chatting regularly
- Interacting professionally
- Acting friendly and reliable
Eventually, they ask for a business introduction. For example:
- “I’m looking for computer equipment suppliers.”
- “Can you introduce me to someone trustworthy?”
- “We have a large government or school contract.”
Because the relationship already feels genuine, the referral happens naturally.
The trap
The scammer then approaches the referred person with a seemingly legitimate business deal:
- Large purchase orders
- Attractive profit margins
- Familiar references
- Official-looking invoices
- Corporate or government claims
After negotiations, the scammer introduces a “secondary supplier” or “special product batch” that requires advance payment. The victim may transfers money because they believe that:
- The deal is legitimate
- The introduction came from a trusted person
- The final customer exists
Then the scammer disappears, after receiving money.
Why this scam is so effective
This attack exploits:
- Trust between family members
- Professional reputation
- Fear of missing business opportunities
- Emotional pressure from “special deals”
- Greed mixed with familiarity
This scam is carefully calculated so that every step feels reasonable.
How to protect yourself
- Never rely solely on personal referrals
- Verify companies independently
- Refuse unusual invoice-merging requests
- Be suspicious of advance payments to third parties
- Confirm contracts through official business channels
- Slow down when large profits appear “too easy”
Professional scammers are patient. They may spend months preparing a single attack.
3. Fake Government & Military Procurement Scams
A similar scam targets small business owners.
Typical scenario
Scammers pretend to represent: Military departments, Government agencies, Schools, Hospitals, or Large organizations. They contact vendors claiming they need bulk purchases such as: Office supplies, Furniture, Electronics, Plastic chairs, Construction materials. The order appears legitimate and valuable. Then the scammer says:
“We also need another product that you don’t sell. We found another supplier already. Can you help combine the invoice?”
Soon afterward:
- A fake supplier contacts the victim
- Payment is requested upfront
- The victim transfers money
- Then Everyone disappears
Why victims fall for it
Because:
- The “customer” sounds official
- The order size feels realistic
- The opportunity seems profitable
- The victim expects reimbursement later
This psychological manipulation is extremely effective.
Defense strategy
- Government organizations rarely operate through informal personal arrangements
- Never pay suppliers on behalf of customers without independent verification
- Verify procurement requests using official government contact channels
- Be suspicious of invoice manipulation requests
4. Caller ID Spoofing & Fake Support Calls
One of the scariest modern scams involves fake phone numbers and spoofed caller IDs.
What is caller ID spoofing?
Scammers, with tech skills, can manipulate what appears on your phone screen. You may receive a call that appears to come from: your bank, the police, tax authorities telecom providers or government agencies. But the displayed number or name is fake.
How they do it
Modern calling systems using VoIP (Voice over Internet Protocol) allow attackers to manipulate caller information. Combined with high tech attack such as Fake BTS systems, the scam can look extremely convincing.
Common scam scenarios
The caller claims:
- Your bank account was hacked
- Your identity is under investigation
- Your SIM card will be disabled
- Your tax records need updating
- Suspicious transactions were detected
Then they pressure you into:
- Sharing OTP codes
- Installing apps
- Clicking links
- Sending money
- Changing passwords
The golden rules
- Never share OTP codes: No legitimate bank or authority should ever ask for your verification code over the phone.
- Hang up and call back manually: If someone claims to represent an organization: End the call –> Visit the official website –> Call the publicly listed number yourself
Never trust incoming caller IDs alone.
Modern scams are no longer based on technical hacking alone. They rely heavily on emotional manipulation and social engineering. Scammers understand human psychology surprisingly well. Often, victims are not careless or unintelligent, they are simply manipulated under pressure.
Scams are evolving faster than ever. Artificial intelligence, voice cloning, deepfakes, caller ID spoofing, and long-term trust manipulation are making fraud far more convincing than traditional scams from the past. The most important defense today is not technology, it is awareness. A few extra minutes spent verifying information can prevent devastating financial losses. Stay skeptical. Stay informed. And most importantly, help educate the people around you, especially older family members who may be more vulnerable to these increasingly sophisticated attacks.